Magento 2 PolyShell exploit lets scammers upload executable files to pub/media/custom_options folder.
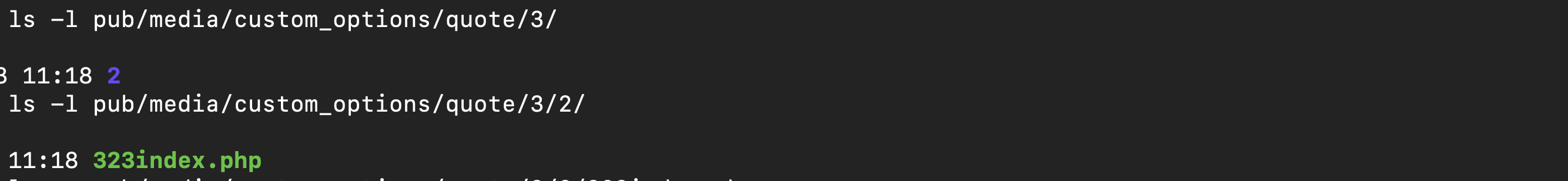
A successful exploit looks like this:
ls -l pub/media/custom_options/quote/3/2/ 323index.php
Then they try to load that file on web:
GET /media/custom_options/quote/3/2/323index.php HTTP/2.0
In this article I’ll show you steps to protect your online store against this attack.
1. Deny web access to all files in pub/media/custom_options folder
No files in /media/custom_options should be visible to the public.
Nginx sample config file that comes with Magento already has it blocked:
location /media/custom_options/ {
deny all;
}If you have Nginx as a web server make sure you have that setting.
For those running Apache the correct .htaccess file is already included:
<IfVersion < 2.4>
order deny,allow
deny from all
</IfVersion>
<IfVersion >= 2.4>
Require all denied
</IfVersion>Confirm the correct configuration, create a test file and try to view it in a browser:
touch pub/media/custom_options/test.php wget www.yourdomain.com/media/custom_options/test.php
You should receive 403: Forbidden response.
2. Make custom_options folder Read-Only
Just like with SessionReaper it makes sense to stop any malicious uploads making a folder read-only.
chmod 444 pub/media/custom_options
Make sure you empty the folder before removing write access.
3. Put Magento Codebase under GIT control
Use git version control and check for suspicious file changes regularly.
git status pub/media/custom_options
You can write a Bash script that git status the whole Magento folder and alerts you if new files appear.
Put it on cron to run twice a day or daily.
That way you can see where scammers add malware and act ASAP.
Summary
PolyShell exploit is widely used on Magento 2 websites.
You can protect your store by:
- Monitoring for new/unwanted file changes
- Making pub/media/custom_options folder read-only
- Denying any web access to /media/custom_options/* URI
If you need assistance securing your website - contact me for a free quote.
Stay safe and Good Luck!
Find this article useful? Share it on LinkedIn with your professional network, spread the knowledge!
If you find this post interesting do not hesitate to sign up for our newsletter and join the 1010 people who receive Magento news, tips and tricks regularly.
Thank You!


